Bugs, hidden cameras, GPS trackers, and spy software are the biggest threats to your privacy now and in the future. Your technology can hear you. It can see you, too. And so can the CIA. At least that is what WikiLeaks revealed last month. Questions about what can be done to prevent this have circulated in the cybersecurity network since then, and WikiLeaks has flirted with the idea of teaming up with some of technology’s biggest (Apple, Samsung, Google, etc.) to stop the CIA’s hacking of private citizens.
Let’s recap the accusations against the CIA: WikiLeaks is claiming the intelligence center can hack into everyday devices, including phones and TVs, to spy on the users. This gives the CIA a huge amount of data to sift through — WikiLeaks leaked almost 9,000 pages of material. While the data did not provide specific information about the number of devices and sources hacked to gain the information, the sheer existence of such programing and tools has private citizens concerned for their security.
Bug sweeps, professionally known as Technical Surveillance Countermeasures (TSCM), are incredibly helpful in revealing whether or not you are being tracked by an unapproved source. Because the goal of a bug sweep is to locate and eliminate (remove or counter the signal) of “bug” devices that are gathering, recording and transmitting your information covertly, they are essential for those who have found evidence that there space is bugged. While common devices may not be able to be stopped just yet from being hacked by the government (though the major tech companies are making fixes to prevent further hacking), you can ensure your property is a safe space.
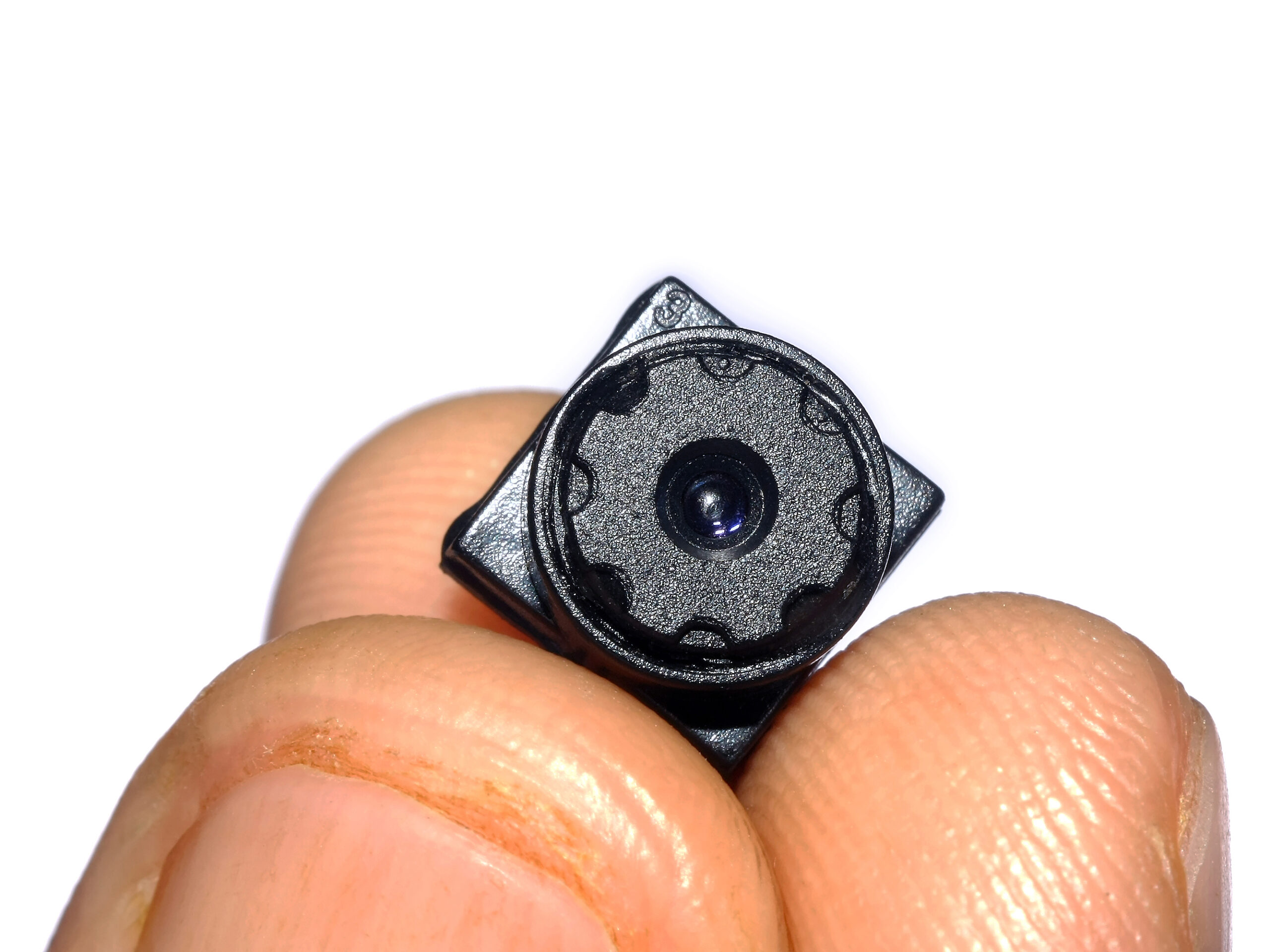
The question is, how can you prevent yourself from being bugged? Having a security expert come in and perform a broad bug sweep can reveal hidden, illegal, and unwanted devices in your home, car, office or other space that may be used to spy on you. These include hidden cameras, GPS trackers, cell phone spy software, tapped landline phone wires and microphones or other audio surveillance devices.
AEGIS Security & Investigations’ bug sweeps are conducted in a variety of environments for a variety of clients. We have provided comprehensive bug sweeps in private estates and personal residences as well as for various business, corporate offices, and government entities, including sole practicing attorneys, law firms, and financial management firms. Bug sweeps can be conducted in offices, vehicles, on a person or in any private space.
An AEGIS Security & Investigations bug sweep is typically conducted after business hours in order to keep from raising suspicion and provide confidentiality to the client. The process involves a total of five steps, which we’ve outlined below.
- AEGIS Security & Investigations bug sweeps starts with a spectrum analyzer examining frequencies emitting from the target area beyond of the normal commercial spectrum. It works by graphing the frequency and power of signals, distortion, harmonics, wave length and other determining factors. The graph resembles that of an oscilloscope with the frequency on the horizontal plane and the amplitude on the vertical plane. This device detects the difference between cell phone transmissions both of the voice and data variety, cordless phones, WiFi signals and bugs transmitting wireless signals.
- Second, the target is examined with a wideband receiver designed to pick up any low power devices that could have been missed by the spectrum analyzer. Low power devices are designed to go short distances, typically point to point. This may include radio waves emitting from smaller, more portable devices. A comprehensive bug sweep is not complete without the use of a wideband receiver.
- Third, electrical outlets are examined for carrier currents that would permit listening through electrical lines. A carrier current is a low power, hard wired audio transmission sent through an electrical line. They do not go long distances, as the current is adjusted as it passes through a transformer. The transmissions can be easily picked up a commercial grade scanner by an individual sitting outside of a building, hence the necessity to examine the outlets during a bug sweep.
- Fourth, a non-linear junction detector is used to locate electrical components of devices whether they are on or off. It blasts a high-frequency radio transmission and from the receiving pad. When it detects a return on the frequency, the operator is alerted to electrical components within the search radius. This device works much like a bat would use echo-location. Some bugs can be set to have burst transmissions or only operate while it is picking up voice or video. This allows us to pick those devices up during our TSCM bug sweep, even when they are off.
- Last, a phone analyzer is used in conjunction with a physical examination of the phone system to detect phone and wire taps. Wiretapping occurs digitized or audio conversations is sent to an unauthorized third party. This may be done through a Trojan horse in a fully digital phone, an inductive coil attached to the handset, a physical recording device, splitting a line, or creating a manual recording. The phone analyzer can assist in detecting if a signal is being rerouted, spliced or copied.
Additional services include computer and IT security strengthening against viruses, Trojan horses, worms and keyloggers. AEGIS Security & Investigations provides custom solutions created for each client by experienced professional in their respective fields. If the bug sweeps yield results requiring further private investigation or security services, clients can rest assured AEGIS is there to help.
AEGIS Security & Investigations is a Los Angeles region company that is licensed and insured in the State of California to provide high-end armed and unarmed regular and temporary off-duty police officers, bodyguards, security officers, loss prevention agents, and event staff. Additionally, we offer services for private investigation, consultation, people tracing, and background investigation. Our trainings and workshops in the field of security licensure and counter-terrorism have been featured in news media and are renowned for their efficacy. For more information or to contact us, visit www.aegis.com.
Authors: Chelsea Turner and Jeff Zisner